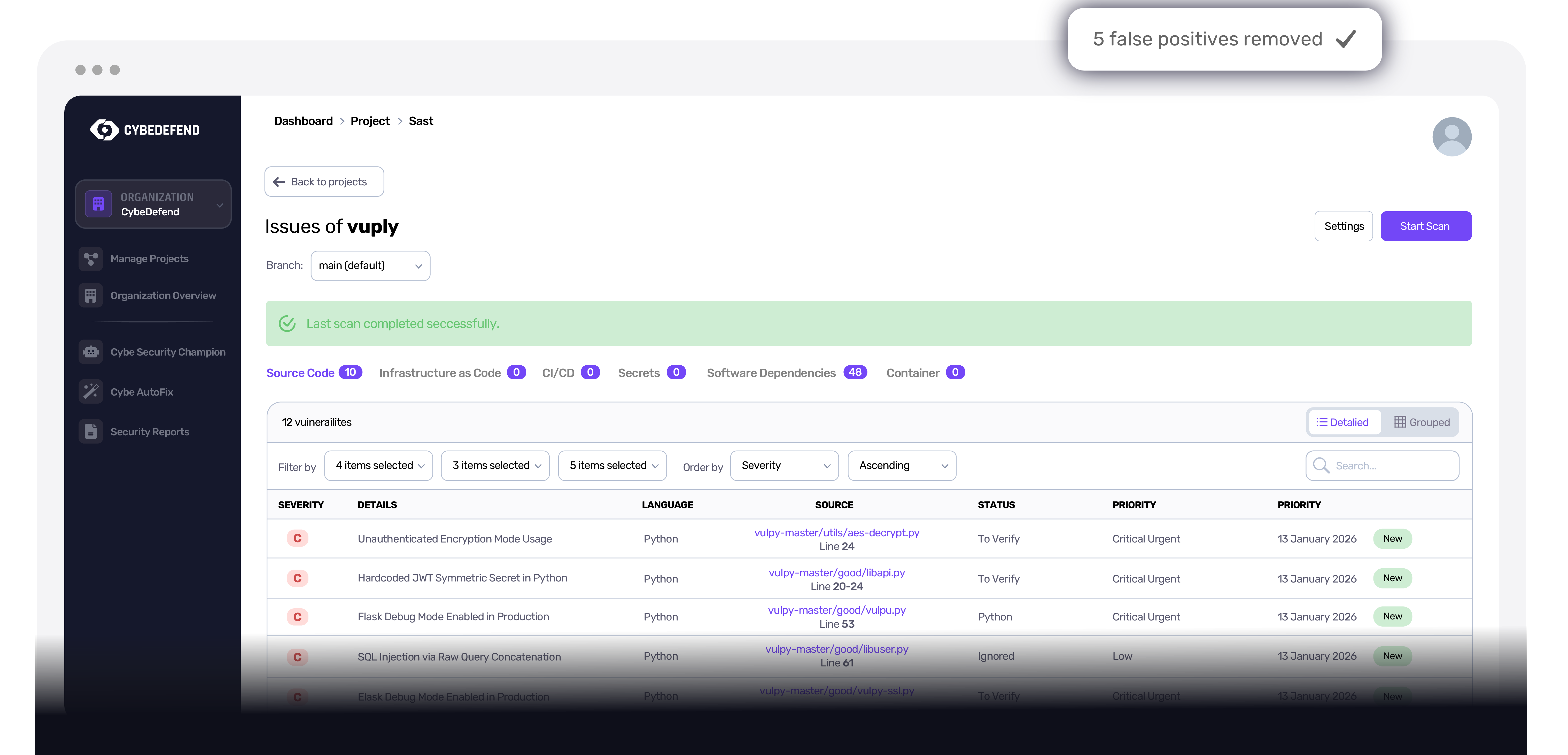
False positives killed at the source
Our knowledge graph distinguishes real threats from false alarms during the scan itself, not after. Up to 90% less noise. Accuracy levels that decades-old AST tools could not deliver.
An autonomous AI agent that analyses, contextualises and prioritises every finding. Knowledge-graph powered, self-hosted, GDPR-native. Up to 90% of false positives killed during the scan, not after.
Traditional tools only look at lines of code in isolation. Cybe Analysis scans differently, it builds a complete map of your application's logic and reasons about it the way a senior engineer would.
We build a complete map of your app's logic, tracking data flow across files through advanced annotation parsing.
Every function, sink, source and framework gate becomes a node. Edges encode reachability, sanitiser coverage and trust boundaries.
It understands how the code is used, allowing it to filter out 90% of irrelevant alerts during the scan itself.
Real session, no edit. Cybe Analysis dedupes, scores and assigns vulnerabilities while you watch.
Each tile is one product capability. And the business outcome it unlocks. We refuse to ship one without the other.
Our knowledge graph distinguishes real threats from false alarms during the scan itself, not after. Up to 90% less noise. Accuracy levels that decades-old AST tools could not deliver.
Each finding ships with an exploitability + reachability + business-impact score and a remediation-complexity estimate. Like a senior AppSec engineer reviewing your queue 24/7. Your team focuses on strategy, not on triaging noise.
Smart parsing + knowledge graph trace vulnerability paths through complex codebases with unprecedented precision. Senior-level expertise scaled to every repository, every language, every framework.
Models run on our infrastructure with zero external API calls. Your code never leaves your region. GDPR · NIS2 · DORA · SOC 2 native. The strictest compliance requirements, met without an asterisk.
Three guarantees the buying committee will ask about. Three answers we can give without an asterisk.
Your data never leaves your infrastructure. Models run inside the EU or US region you chose at signup.
100% in-house development, no external API dependencies. No OpenAI, no Anthropic, no third-party LLM in the analysis path.
Advanced code parsing and analysis technology, built and operated by us, auditable, reproducible, sovereign.
A traditional SAST tool flags every pattern match it sees, leaving developers to filter the 90% of false positives. Cybe Analysis builds a knowledge graph of your application, function calls, taint flow, framework gates, and only surfaces findings that are reachable, exploitable and material in your business context. The 90% of noise is dropped during the scan itself, not after.
Cybe Analysis runs on our self-hosted AI infrastructure (EU or US region, isolated). It does not call external LLM APIs (OpenAI, Anthropic or otherwise). Your code, vulnerabilities and analysis stay inside the region you pick at signup.
Each finding ships with: a risk score (exploitability + reachability + blast radius + business impact), a remediation-complexity estimate, a recommended owner, and a written rationale that a junior engineer can act on without escalation. That is the cognitive output we benchmark against a senior AppSec engineer.
Cybe Analysis runs on CybeDefend's own scanners, SAST, SCA, IaC, container and secret engines built in-house, and applies a reachability + business-context layer over their output. The value is the analysis on top of our scanners, not third-party SARIF ingestion. Teams that adopt Cybe typically replace their legacy SAST/SCA outright; you get one source of truth, one dedup graph, and ~90% fewer false positives.
Median diff scan completes in seconds. A full-repository first-time scan typically completes in minutes. Subsequent runs only re-analyse changed code paths, so steady-state cost is bounded by your commit cadence, not by repository size.
Yes. EU customers run on the EU region (GDPR / DORA / NIS2 native). US customers run on the US region (SOC 2 Type II, HIPAA-ready). Data residency is hard, your findings never cross regions, ever. Self-hosted deployments are available for highly regulated environments.
The Security Code Knowledge Graph is CybeDefend's unified representation of your codebase as a queryable property graph. Every source file, function, data flow, dependency, infrastructure resource and secret reference becomes a node; their relationships (call edges, taint-flow edges, import edges, exploit paths) become typed edges. When a scan runs, we query this graph rather than pattern-matching on raw text, which is why we catch multi-file taint paths, cross-service business logic flaws, and reachable CVEs that single-file SAST misses entirely. The graph is computed once per repository and updated incrementally on each agent diff, keeping P95 query time under 1.2 seconds on 100k-LOC repos. It also powers deduplication across SAST, SCA, IaC, container and secret findings, one graph, one source of truth, zero duplicate alerts for the same underlying flaw.
No credit card. No setup call. Pick your agent, paste the command, and Cybe enforces your rules from the very next prompt.
claude mcp add cybedefend --transport http https://mcp-eu.cybedefend.com/mcpHosted MCP, no install. Just register the URL with your agent.